A few days ago, I received a call from one of our domestic sales reps, Jon, talking about some potential sales leads he uncovered while attending a conference on cyber security a few days prior. I listened as Jon talked about a growing demand for RF products in the cyber security industry and the potential for NuWaves to expand its product applications.
Cyber security is not a field that my co-workers nor I would use to describe NuWaves’ target demographic, but perhaps the RF industry needs to take another look at its relationship with cyber security and reevaluate how this relationship may evolve in the future. Today, I want to discuss why the relationship between electronic warfare and cyber security has suddenly changed over the past decade, and what this could mean for companies in the RF industry going forward.
At the onset of the Civil War in 1861, the Union had an immediate advantage over the Confederacy with an extensive telecommunications infrastructure that extended all throughout the northern states. In an attempt to level the playing field cavalry men from the Confederacy routinely switched military telegraph traffic to the wrong destinations, transmitted false orders to Union commanders, and cut the wires to deny the information to the Union forces. [1]
The importance of controlling the lines of communication was understood during the Civil War and continues to be one of the top priorities for most countries’ defense strategies today. During Operation Desert Shield in 1991, the first priority of the U.S. armed forces was disabling Iraq’s Air Force and anti-aircraft facilities – the second was destroying Iraq’s telecommunication infrastructure. [5]
In 1861, disabling your enemy’s lines of communication meant destroying the telegraph cables that provided the only means for quick, long distance communication. During the 1st Gulf War in 1991, the fight for telecommunications control was surprisingly similar to what it was in 1861. By this time the internet had been around for a while, but most telecommunications technology still relied on wired connections to transmit large amounts of data and information. Both sides were spending resources to protect and destroy actual telecommunication lines and infrastructure, just like the Union and Confederacy were during the Civil War.
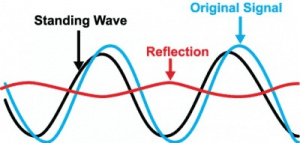
Fast forward to 2016 and things have changed dramatically. Controlling your enemy’s lines of communication is a lot more challenging now that wireless broadband networks have replaced the need for physical telecommunication lines, offering the air around us as a means to transmit data around the world. Yes, the internet allowed us to easily send data around the world, but it wasn’t until we paired the internet with the RF spectrum that we could begin building the wireless broadband networks that would finally change how the fight for telecommunications control would play out.
Before the RF spectrum could be paired with the internet, some technological advancements in the industry had to come first. Advancements in RF technology have continued along at an exponential rate since 1888, when Heinrich Hertz became the first person to decisively prove the existence of electromagnetic waves. By 1894, the first wireless telegraph was being developed and it was only a year later, in 1895, when an Italian inventor sent and received the first radio signals in Italy.
By only 1901, the first transatlantic radio signals were already being broadcasted. Jump ahead to 1988 where Classic WaveLAN’s wireless broadband network successfully transmitted data at speeds of 2 Mbit/s over its wireless network. [7] To put 2 Mbit/s into perspective, this article in its Microsoft Word version is just over 2 Mbits. Fast forward again to February of 2016 where NTT DoCoMo and Ericsson successfully achieved a cumulative 20 Gbit/s data transfer rate at 5 GHz frequency range with two simultaneously connected wireless mobile devices.[6]
Consistent advancements in RF technology have allowed tech manufacturers to confidently integrate the RF spectrum into their products, dumping Ethernet ports for the RF spectrum as a means to access the internet wirelessly. Smart phones and tablets for years have relied on the RF spectrum for wireless internet access and have even started using the RF spectrum as a means to supply wireless power.
The Internet of Things (IoT), mobile money transactions (Venmo, PayPal), social interaction (Facebook, Instagram, LinkedIn), transportation (Uber/Lyft), driverless cars (WAYMO); all of these services are only possible to the extent that they exist today thanks to the integration of the RF spectrum in modern technology, providing us with the telecommunications infrastructure of the 21st century. These events and the history of communications is what has caused electronic warfare what it is today. With the continued expansion of the IoT and all of the services it has to offer, it will become that much imperative to win the battle of electronic warfare.

Services like Uber, Venmo, and Twitter depend on the availability of high-speed wireless networks to operate
One major change that wireless broadband networks provide to the telecommunications infrastructure is that they require significantly less infrastructure to function. Additionally, the infrastructure will continue to get smaller in size over time due to the continuously higher frequency ranges that are used to transmit data. Wireless broadband has made it easier than ever before for isolated communities and individuals to stay connected to the telecommunications infrastructure, since airwaves have replaced the expensive communication lines that were once needed to stay connected.
But easy access to a communications network is naturally unbiased – if it is easy for isolated communities and individuals to connect to the telecommunications network, then it will most likely be easy for motivated individuals and organizations with malicious intentions to access the network as well. Enemies of the United States will look at Cyber Electronic Warfare as a means to attack our RF spectrum and the computers that rely on it for internet access.
Figuring out how to protect our RF spectrum from potential threats presents a range of new challenges that require specifically engineered solutions. Companies in the cyber security industry for years have fought to protect our telecommunications network from viruses and malware that target our computers and the information they store. But enemies will increasingly look to disrupt our telecommunications network via a second method – by targeting the RF spectrum that facilitates the wireless transfer of data to and from our computers. Companies in the RF industry such as NuWaves Engineering will be asked to engineer solutions that protect our RF spectrum from potential threats abroad electronic warfare attackers, without disrupting the wireless broadband networks that we depend on.
References
[2] https://en.wikipedia.org/wiki/Wireless_broadband
[4] https://www.helmholtz.de/en/technology/the-fastest-wireless-data-transmission-5644/
[1] http://calhoun.nps.edu/bitstream/handle/10945/2642/06Sep_Kucukozyigit.pdf?sequence=1
[5] https://en.wikipedia.org/wiki/Gulf_War#Air_campaign
[6] https://en.wikipedia.org/wiki/5G